ULedger Blockchain Secure, Tamper-Proof Enterprise Data Infrastructure
At the core of our platform is a suite of advanced, composable modules. This allows you to construct solutions and automate workflows with granular precision, delivering value for your specific operational needs.


Data Integrity
Immutable
Interoperable
Flexible
Secured
Efficient
Auditable
Data Integrity
Immutable
Interoperable
Flexible
Secured
Efficient
Auditable
Data Integrity
Immutable
Interoperable
Flexible
Secured
Efficient
Auditable
Data Integrity
Immutable
Interoperable
Flexible
Secured
Efficient
Auditable
Data Integrity
Immutable
Interoperable
Flexible
Secured
Efficient
Auditable
CAPABILITIES
Where Our Features Become Your Benefits
Quantum Cryptography
Future Proof Data Integrity and Security
Eliminate Volatile Spend
Wallet-Based Access Control
Dynamic Data Governance
Customizable Business Logic & Rules
Verification while keeping Data Private
Key Features
Strategizing Your Digital Assets
Non-Crypto Centric
Predictable costs with our core technology, independent of cryptocurrency.
Custom Tokenization
We create custom tokens for flexible solutions on demand.
Enterprise Focused
ULedger offers both crypto-independent and token capable solutions.
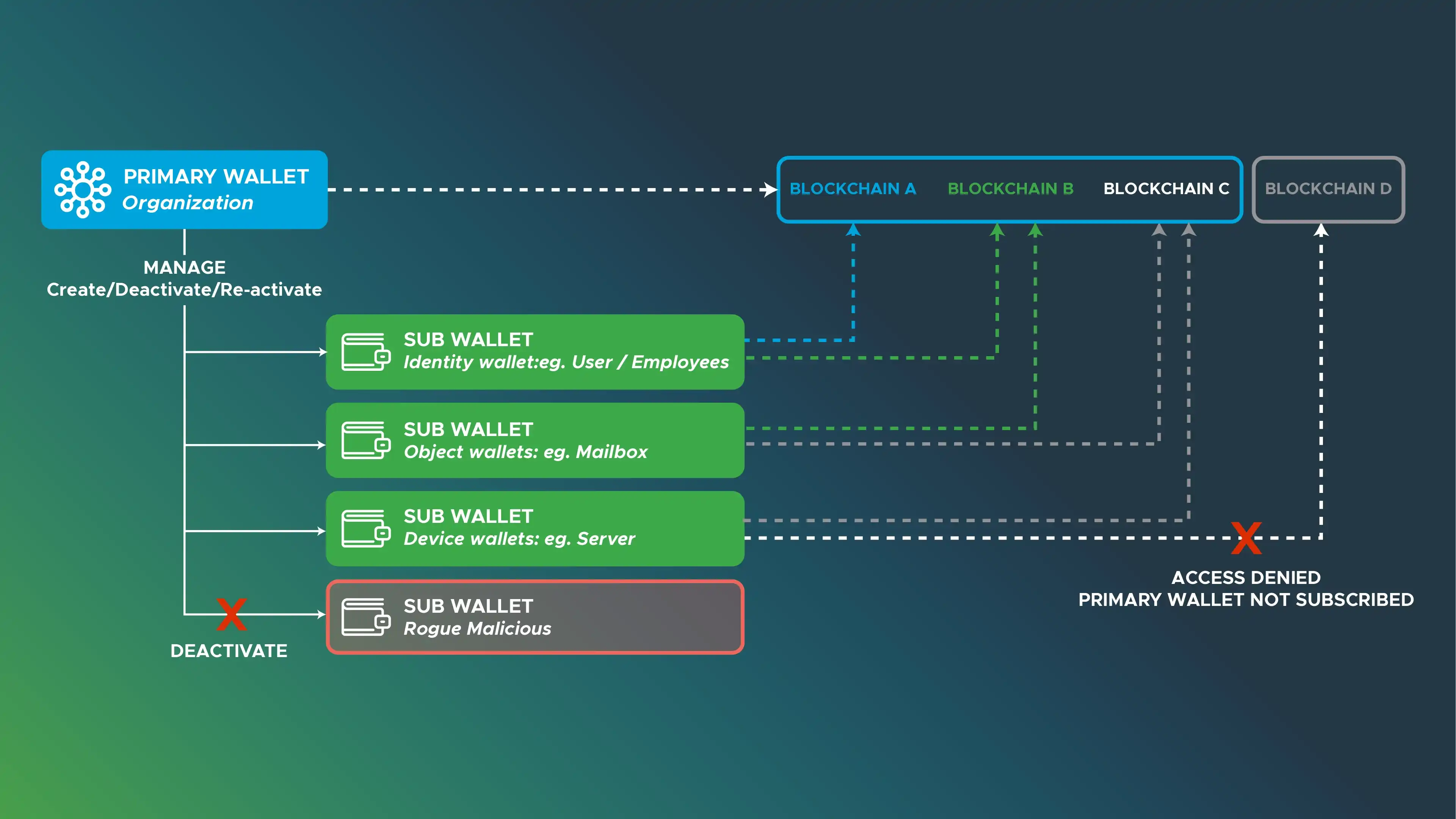
Data Governance
Wallet-Based Access Control
A simple, secure way to implement data access controls on your blockchain data.
An effective Wallet Framework
Meet our Central and Satellite wallet system - a comprehensive way of organizing permissions within a blockchain and furthermore, a way to remove access in real time to wallet holders that do not follow the established guidelines.

INTEROPERABILITY
Cross - Merkleization
Our patented technology for reliable blockchain trust.
Blockchain Network Independence
Maintains each blockchain's autonomy while enabling inter-chain verification.

Privacy-First Design
Validates blockchain state without exposing sensitive transaction details.

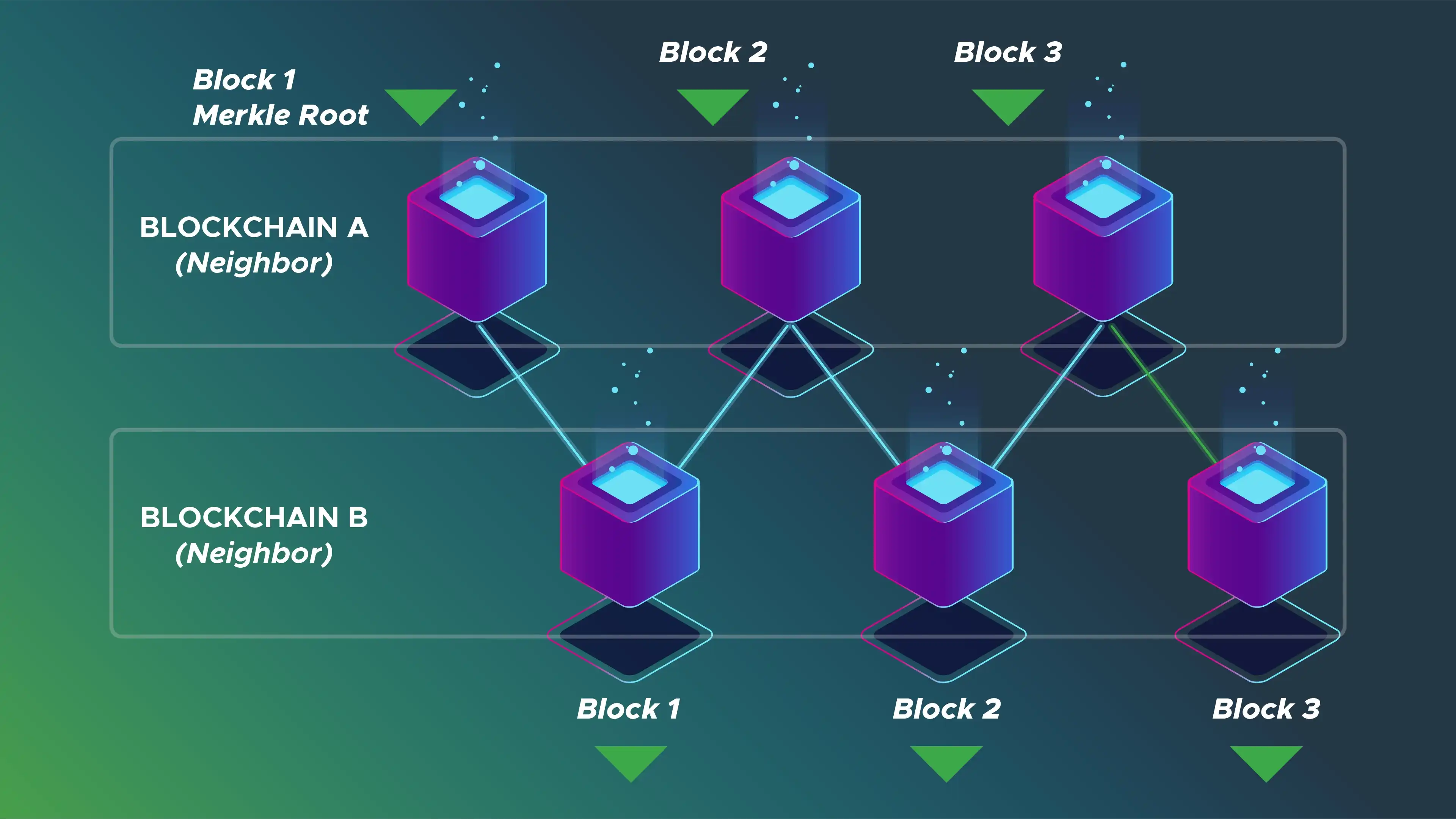

HOW IT WORKS
The Cross Merkleization Process
Proof Generation

Digest Sharing

Trust Establishment


WEB ASSEMBLY
Smart Contracts
Effortless automation and support for complex workflows
Powerful Secure Runtime
Run complex automations and advanced workflows on our robust WebAssembly virtual machine, ensuring high efficiency and security without surprise scaling costs.
Develop With Ease
Empower your technical team to build quickly and effectively using the familiar programming languages they already master, like Go, TypeScript, and Python.
Contracts That Evolve
Keep your solutions adaptable and up-to-date. Our upgrade-ready architecture allows for seamless and straightforward updates to your smart contracts as your needs evolve.
FAQ's
Frequently Asked Questions
What Are Quantum Safe Security Solutions?
Quantum-safe security solutions use cryptography designed to resist attacks from future quantum computers. They protect sensitive data even if current encryption standards become vulnerable.
How Does Blockchain Ensure Data Integrity in Enterprise Systems?
Blockchain creates immutable, time-stamped records that cannot be altered without detection. This makes it easier to prove what happened and when.
What Are Post Quantum Cryptography Solutions for Long-Term Protection?
Post-quantum cryptography solutions use new algorithms built to withstand quantum-level computing attacks. They help organisations protect data for decades, not just years.
What Is a Quantum Safe Blockchain?
A quantum-safe blockchain combines distributed ledger architecture with quantum-resistant cryptography. It keeps records tamper-evident while preparing for future threats.
Post Quantum Cryptography vs Traditional Encryption: What’s the Difference?
Traditional encryption can be broken by powerful quantum computers in the future. Post quantum cryptography is designed to stay secure even in that scenario.
How Does Blockchain Improve Data Integrity in Regulated Industries?
It creates permanent audit trails that support compliance and investigations. Regulators can verify records without relying on editable internal logs.
Why Do Enterprises Need Quantum-Resistant Cryptography Today?
Data stolen today can be decrypted later when quantum technology matures. Quantum-resistant cryptography prevents that long-term exposure.
How Can Blockchain and Post-Quantum Cryptography Work Together?
Blockchain secures and timestamps records, while post-quantum cryptography protects the underlying signatures and keys. Together, they create durable, tamper-evident systems.
What Are the Risks of Quantum Computing to Current Encryption Methods?
Quantum computers could break widely used public-key encryption algorithms. That would expose stored data, digital signatures, and authentication systems.
How Do Quantum Safe Blockchain Solutions Protect AI Systems and Data Provenance?
They anchor AI inputs and outputs with cryptographic proofs that cannot be altered later. This supports traceability, auditability, and trust in automated decisions.